PandaDoc stores document data such as metadata, activity, original files, and customer’s data in different locations while also compiling and generating documents when requested. All data in each location is encrypted at rest with AES-256 and sophisticated encryption keys management.
Get enterprise-grade security for your most sensitive agreements
Our e-Signature software is E-SIGN, UETA and HIPAA compliant. It’s also backed by SOC 2 certification so you can sign with total confidence.

U.S. ESIGN Act and UETA
The U.S. Electronic Signatures in Global and National Commerce (ESIGN) Act and the Uniform Electronic Transactions Act (UETA) each require four conditions for a valid electronic signature: (a) intent to sign, (b) consent to do business electronically, (c) association of the signature with the record, and (d) retention of records. PandaDoc ensures compliance with these requirements under U.S. ESIGN and UETA laws.

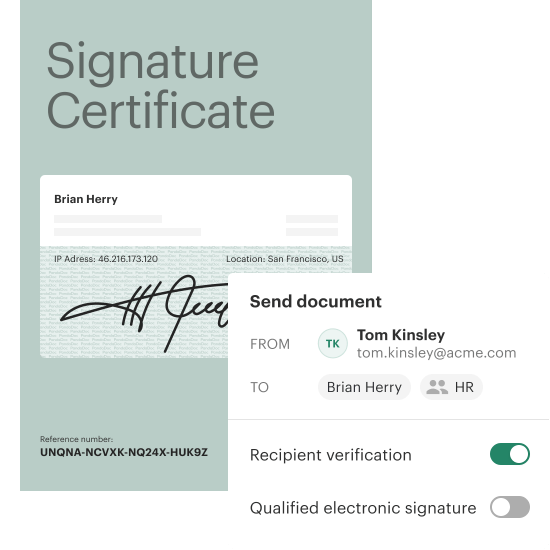
eIDAS and QES
The eIDAS Regulation 2014/910 establishes the framework for the legality of the three types of electronic signatures in the EU and UK.: simple electronic signatures, advanced electronic signatures (AES), and qualified electronic signatures (QES). QES is the highest standard, and Pandadoc provides QES-level signatures.

SOC 2 Type II
PandaDoc is SOC 2 Type II certified. We can provide an SSAE 18 SOC 2 report and attestations of compliance, upon request. PandaDoc services are hosted on the Amazon AWS platform and this document details the ways in which we leverage the massive investments that Amazon continues to make in security to the benefit of our customers.

GDPR
PandaDoc data centers (handled by Amazon AWS) are state of the art, utilizing innovative architectural and engineering approaches. Amazon has many years of experience in designing, constructing, and operating large-scale data centers. This experience has been applied to the AWS platform and infrastructure.

CCPA
The California Consumer Privacy Act (CCPA) establishes consumer privacy rights for California residents and regulates businesses handling personal information. As the first U.S. consumer privacy law, it’s comparable to the EU’s GDPR. Effective January 1, 2020, the CCPA has been amended by the CPRA as of March 29, 2023. PandaDoc is CCPA compliant.

Data Privacy Framework
The Data Privacy Framework (DPF) Program, created by the U.S., EU, UK, and Swiss authorities, allows U.S. organizations to securely transfer personal data from the EU, UK, and Switzerland while ensuring compliance with their laws. The EU confirms that the EU-U.S. DPF ensures adequate protection, enabling safe data flows. PandaDoc is a certified participant in the EU-U.S. DPF and its UK and Swiss extensions.

HIPAA
PandaDoc is fully committed to helping healthcare providers protect patients’ healthcare information when sending ePHI via PandaDoc. PandaDoc is compliant with HIPAA and the Privacy Rule, as well as the Administrative Safeguards, Physical Safeguards and Technical Safeguards of the Security Rule.

FERPA
PandaDoc helps schools facilitate electronic communication between educators, administrators, and school districts and parents and students in full compliance with FERPA (20 U.S.C. § 1232g; 34 CFR Part 99) as to protect the privacy of student education records.

PCI-DSS
PandaDoc offers integrations with payment processors that offer payment processing via credit cards, but does not allow storage of PCI data in its platform.

Data residency in US or EU
Choose where your data gets stored and processed. PandaDoc provides the flexibility your business needs to utilize these two equally secure locations.

Third-party Subprocessors
PandaDoc currently uses third-party Subprocessors to provide various business functions after due diligence to evaluate their defensive posture and executes an agreement requiring each Subprocessor to maintain minimum acceptable security practices.
Software security
Servers and networking
All servers that run PandaDoc software in production are recent, continuously patched Linux systems. Additional hosted services that we utilize, such as Amazon RDS, S3 and others, are comprehensively hardened AWS infrastructure-as-a-service (IaaS) platforms.
Storage
Coding and testing practices
PandaDoc leverages industry standard programming techniques such as having a documented development and quality assurance processes, and also following guidelines such as the OWASP report, to ensure that the applications meet security standards.
Employee access
We follow the principle of least privilege in how we write software, as well as the level of access. Employees are also instructed to use this principle when resolving customer support requests and when diagnosing possible software bugs that arise during development of new features.
Isolated environments
The production network segments are logically isolated from other Corporate, QA, and Development segments.
Customer payment information
System monitoring and alerting
At PandaDoc, the production application and underlying infrastructure components are monitored 24/7/365 days a year, by dedicated monitoring systems. Critical alerts generated by these systems are sent to 24/7/365 on-call DevOps team members and escalated appropriately to operations management.
Service levels and backups
PandaDoc infrastructure utilizes many layered techniques for increasingly reliable uptime, including the use of auto-scaling, load balancing, task queues, and rolling deployments. We do full daily automated backups of our databases. All backups are encrypted.
Vulnerability testing
Web application security is evaluated by the development team in sync with the application release cycle. This vulnerability testing includes the use of commonly known web application security toolkits and scanners to identify application vulnerabilities before they are released into production.
Application architecture
The PandaDoc web application is multi-tiered into logical segments (front-end, mid-tier, and database), each independently separated from each other in a DMZ configuration. This guarantees maximum protection and independence between layers.
Identity Verification
Add a robust layer of security to your documents with PandaDoc’s Identity Verification options. Choose from four flexible methods: passcode verification, SMS verification, knowledge-based authentication (KBA), and ID Check. These options help ensure that only verified recipients can access sensitive information, supporting your compliance and security needs. Click here to learn more about PandaDoc’s Identity Verification offerings.
Responsible Vulnerability disclosure
In case you found a vulnerability, please follow Responsible Vulnerability Disclosure Process to report it to our Security team.